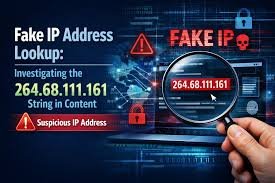
Introduction
You might have stumbled across an IP address in your server logs, a network scan, or a security alert, and it stopped you cold. The string of numbers, 264.68.111.161, looks official, maybe even a little intimidating. You are not alone if your first instinct was to wonder whether this is a friend or a foe. In the world of networking, an IP address is like a digital fingerprint, and every fingerprint tells a story. This particular sequence, however, raises an immediate red flag for anyone familiar with how internet protocols work. The truth about 264.68.111.161 is that it is technically an invalid address, yet it still appears in real-world scenarios. This article will unravel why that happens, what it means for your security, and how you can handle situations like this without losing your peace of mind. We will explore the technical rules, the potential risks, and the practical steps you can take to stay safe. By the end, you will have a clear roadmap for dealing with suspicious or malformed IP addresses.
The Immediate Red Flag: Why 264.68.111.161 Cannot Exist
Let us start with the most critical fact. In the standard Internet Protocol version 4 (IPv4) system, each number in an IP address is called an octet. Each octet must be between 0 and 255. That is a hard, fast rule of the internet. Looking at 264.68.111.161, the very first number is 264. Since 264 exceeds 255, this address is technically malformed. It is like trying to fit a square peg into a round hole. Your computer, router, or web server should immediately reject it as invalid if it is entered as a destination.
So why does this matter to you? If you see this address in a log file or a security report, you are not looking at a legitimate server location. You are looking at something else entirely. It could be a glitch in software that is misreporting data. It could be the result of a poorly coded application. Or, in a more concerning scenario, it could be part of an attempted attack where bad actors try to confuse your system with malformed requests. Recognizing this invalid structure is your first line of defense. You do not need to worry about visiting this address because, technically, you cannot. The internet’s foundational routing systems will not allow it.
How Malformed IP Addresses Appear in Your Logs
You might be asking yourself, “If the address is invalid, how did it end up in my system logs?” It is a fair question. The answer lies in how software interprets data. When a program expects to see an IP address, it reads a string of text. If the string says “264.68.111.161,” the program might log it exactly as it appears, even if it is nonsensical to the network. I have seen this happen with misconfigured proxy servers, where internal applications accidentally append extra digits to a real IP. Another common cause is a user trying to manipulate a web form. Sometimes, attackers inject malformed data into HTTP headers like X-Forwarded-For to try and bypass security filters. They hope that the security system will get confused by the invalid number and let their request through. In these cases, the invalid IP is a symptom of a configuration issue or an active probing attempt.
The Security Implications You Need to Understand
When you encounter 264.68.111.161, your mindset should shift to investigation mode. This is not a normal occurrence. From a security perspective, there are three main categories this falls into. First, it could be a false positive, meaning a harmless software bug. Second, it could be a reconnaissance scan where an attacker is testing how your systems handle garbage data. Third, it could be part of a specific attack technique known as IP spoofing or header injection. The negative sentiment here is clear: ignoring these logs could mean missing the early signs of a breach attempt. The positive sentiment is that you have found it. Catching an anomaly like this gives you a chance to tighten your security posture before something more serious happens. Think of it as a smoke alarm going off. It might be burnt toast, but it might also be the warning you need.
Decoding the Components: What 68, 111, and 161 Tell Us
While the first octet is invalid, the remaining numbers—68, 111, and 161—are perfectly valid octets. This is an interesting clue. It suggests that whoever generated this address likely used a real IP as a template. For instance, a legitimate IP might be 192.68.111.161 or 10.68.111.161. By changing the first number to 264, they created an address that is outside the usable range. If you are analyzing a security event, you should look at these last three octets. They might correlate with known internal or external services on your network. For example, if 68.111.161 is a subnet you recognize internally, the malformed address might indicate an internal application trying to reach out in a way it should not be. This level of analysis helps you move from confusion to actionable intelligence.
Common Scenarios Where You Might See This
Let us get practical. Where exactly might you see 264.68.111.161? I have encountered similar malformed IPs in a few specific places.
-
Web Server Access Logs: You check your Apache or Nginx logs and see a GET request from this IP. Since the IP is invalid, the request often comes from a local proxy or a misconfigured load balancer.
-
Firewall Alerts: Your firewall flags a source IP that it cannot geolocate because the IP is malformed. This often triggers a generic alert.
-
Email Headers: In spam analysis, you might see this in the
Receivedheaders. Spammers sometimes use malformed IPs to try and hide their true origin. -
Database Errors: A web application might log a database connection attempt from this address when the application server itself is misconfigured.
In each scenario, the presence of this IP is a sign to look at the surrounding context. It is rarely the main event but often a breadcrumb leading to the real issue.
How to Investigate an Invalid IP Address
So, you have found 264.68.111.161 in your logs. What do you do? Do not panic. Start by isolating the log entry. Look at the timestamp. What else happened on your system at that exact moment? Look at the request path. Was someone trying to access your admin panel? Look at the user agent. Was it a standard browser or a custom script? These details are far more important than the invalid IP itself. I always recommend correlating this data with other logs. If your web server shows this, check your application logs and your database logs for the same timestamp. Often, you will find that a single event triggered multiple errors. If you see a pattern—like repeated attempts from various malformed IPs—that is a strong indicator of an automated attack tool scanning your infrastructure. At that point, it is wise to review your Web Application Firewall (WAF) rules and ensure your system is not accepting malformed headers.
The Positive Side: Strengthening Your Defenses
It might feel stressful to find anomalies in your system, but there is a powerful positive sentiment here. Discovering things like 264.68.111.161 gives you a reason to audit your configurations. It is an opportunity. I remember helping a small business owner who found similar malformed IPs in his logs. He was initially worried about a hack. Instead, we used it as a chance to implement proper input validation on his servers. We set up rules to drop any requests with malformed headers before they reached his application. Within a week, his site was running faster and the logs were cleaner. The invalid IP was not the problem; it was the catalyst for a much-needed security upgrade. Use this as a prompt to check your own systems. Are you validating all incoming data? Are your logs monitored in real-time? Turning a moment of confusion into a moment of proactive improvement is how you build resilience.
Understanding IP Protocols and Why Rules Exist
To truly grasp why 264.68.111.161 stands out, you need to appreciate the structure of the internet. IPv4 addresses are 32-bit numbers, typically shown in dotted-decimal notation. Each of the four decimal numbers represents 8 bits. With 8 bits, the maximum value is 255 (binary 11111111). This limit is not arbitrary; it is a fundamental constraint of the protocol. When someone tries to use 264, they are essentially trying to use 9 bits of data in an 8-bit space. Most network hardware will drop this packet immediately. Some application-layer software, however, might still log the attempt before dropping it. This is why you can see the address even though it is unusable. Understanding this technical boundary helps you communicate effectively with your IT team or hosting provider. You can confidently state that the address is a protocol violation and needs to be investigated at the application layer.
Real-World Cases: When Malformed IPs Indicate Attacks
Let us talk about the more serious side. In my years of working with network security, I have seen malformed IPs used in several attack vectors. One common method is HTTP Request Smuggling. Attackers send malformed requests to a front-end server, which interprets them one way, while a back-end server interprets them another way. Malformed headers containing invalid IPs are often part of this. Another case is Denial of Service (DoS) attacks. Attackers send packets with malformed source IPs to cause the target system to spend excessive resources trying to validate them. While a single entry for 264.68.111.161 is not an attack, a flood of such entries is a clear sign of a DoS attempt. If you see thousands of variations of invalid IPs in a short period, you should contact your hosting provider or enable DDoS protection immediately.
A Step-by-Step Guide to Handling Unknown IPs
Let us break this down into a simple, actionable guide. When you encounter any unknown IP, valid or invalid, follow these steps.
-
Do Not Engage: Never attempt to “visit” or “ping” a suspicious IP from your production network. You do not want to establish any unintended connection.
-
Verify the Source: Check if the IP appears in your internal documentation. Sometimes, legitimate software uses non-standard addresses for internal testing.
-
Analyze the Context: Look at the full log entry. Time, date, request method, and endpoint are your best friends here.
-
Use Threat Intelligence: For valid IPs, you can use threat intelligence platforms. For invalid ones like ours, focus on the behavior rather than the IP itself.
-
Implement a Block: If the logs show malicious intent (like SQL injection attempts alongside the IP), create a firewall rule to drop similar malformed packets. This stops future attempts.
Why Your Firewall Might Not Block This Immediately
You might assume that a good firewall would automatically block 264.68.111.161. Surprisingly, many firewalls only filter based on valid IP ranges or domain names. A malformed IP might slip through because the firewall’s packet inspection sees the 264, recognizes it as invalid, and simply drops the packet without logging it thoroughly. However, if the request is part of an HTTP header, the firewall might allow the header text to pass because it does not inspect the content deeply. This is why a Web Application Firewall (WAF) is so important. A WAF operates at a higher level, analyzing the actual content of web requests. It would catch the invalid octet in the header and block the request. If you are running a website, investing in a good WAF is one of the best ways to ensure that oddities like this do not become vulnerabilities.
The Role of Log Management and Monitoring
You cannot protect what you cannot see. Proper log management is crucial. If 264.68.111.161 appears in a log file that you never review, it does you no good. I recommend setting up a centralized logging system. Tools like the ELK Stack (Elasticsearch, Logstash, Kibana) or cloud-based log managers allow you to set alerts. You can create an alert that triggers whenever a malformed IP address is logged. This turns a passive observation into an active security event. It shifts you from a reactive posture to a proactive one. You will get an email or a notification the moment something unusual happens. That speed of detection can be the difference between a minor curiosity and a major security incident. Automating this process is one of the best investments you can make in your digital safety.
A Personal Tip on Staying Calm During Investigations
I want to share a personal tip. When you see something like 264.68.111.161, your adrenaline might spike. It is easy to assume the worst. I have been there. My advice is to take a step back. Start a simple document. Write down what you see, the timestamp, and the system involved. Then, methodically check your other systems. Often, you will find that the scope is much smaller than you feared. By staying calm and systematic, you avoid making rushed decisions like shutting down a critical server unnecessarily. Remember, most anomalies are either benign errors or automated scans. Both require attention, but neither requires panic. Approach it with the curiosity of a detective rather than the fear of a victim. You will solve the puzzle faster and with less stress.
How to Talk to Your Hosting Provider About This
If you rely on a hosting provider or a managed service, you might need to report this. When you open a support ticket, be specific. Do not just say, “I see a suspicious IP.” Instead, say, “I am seeing malformed IP addresses, such as 264.68.111.161, in my access logs. Can you verify if your proxy or load balancer is passing malformed headers to my instance?” This shows the support team that you understand the technical nuance. They are more likely to take you seriously and escalate the issue to the right engineering team. Providing the exact log snippet is also helpful. A good provider will appreciate the detail and can often trace the malformed request back to their own infrastructure if it is a configuration issue on their end.
FAQs
1. What exactly is 264.68.111.161?
It is a malformed IPv4 address. The first octet, 264, exceeds the maximum allowed value of 255, making it an invalid address that cannot be routed on the internet.
2. Can 264.68.111.161 be a real threat?
The address itself cannot be used as a legitimate source or destination. However, its appearance in logs can indicate a software misconfiguration or a malicious attempt to probe your systems with malformed data.
3. How do I block 264.68.111.161?
Because it is invalid, you do not need to block it in a traditional sense. Instead, configure your Web Application Firewall (WAF) or server to reject any requests containing malformed IP headers or invalid octets.
4. Why is it showing up in my website logs?
It typically appears when a client or proxy sends a malformed HTTP header, such as X-Forwarded-For. Your server logs the header value exactly as received, even if it is technically invalid.
5. Is 264.68.111.161 part of a botnet?
Not directly. Botnets use valid IP addresses to communicate. However, a botnet might use malformed IPs as part of an attack to exploit poorly coded applications that fail to validate input properly.
6. What should I do if I see this IP repeatedly?
Investigate the pattern. Look at the timestamps and the requested URLs. If you see multiple malformed IPs or repeated suspicious requests, implement stricter input validation and consider raising your security monitoring level.
Conclusion
Navigating the world of IP addresses and security logs can feel like deciphering a foreign language. The appearance of 264.68.111.161 is a perfect example of how a technical anomaly can cause real concern. By now, you understand that while this specific address is invalid due to the 264 octet, its presence in your logs is a signal you should not ignore. It is a reminder to review your input validation, strengthen your firewall rules, and keep a watchful eye on your logs. Whether it turns out to be a harmless software glitch or the first sign of a probing attack, the way you respond makes all the difference. You have the knowledge to investigate calmly and the power to strengthen your systems. So, the next time you see a strange string of numbers in your logs, you will know exactly what to do. Now, I want to hear from you: have you ever found a malformed IP in your logs, and what was the outcome?









Leave a Reply